Press Release
WarRin Protocol: A point-to-point anonymous privacy communication system
Dr.WarRin
Summary
This white paper provides an explanation of the WarRin protocol and related blockchain, point-to-point, network value, transport protocol, and encryption algorithms. The limited space will highlight the WRC allocation scheme and purpose of the WarRin Protocol Token, which is important for achieving the WRC’s stated objectives. This white paper is for informational purposes only and is not a promise of final implementation details. Some details may change during the development and testing phases.
1. Introduction
Traditional centralized communication systems such as WeChat,WhatsApp, FacebookMessage,Google Allo,Skype face a range of problems, including government surveillance, privacy breaches, and inadequate security, and the WarRin protocol proposes apoint-to-pointencrypted communications system that leveragesblockchain technology, combined with Double Ratc het algorithms, pre-keys, and extended X3DH handshakes. The WarRin Protocol uses The Generalized Directional Acyclic Graph and Curve25519,AES-256, and HMAC-SHA256 as the pronamor, allowing each account to have its own unique account chain, providing unlimited instant communication between points and unlimited scalability, anonymity, integrity, consistency, and asynchronousness.
2. WarRin Protocol communication system
2.1 Two types of communication
The Waring Protocol communication system divides chat channels into two types.
Two modes of communication
- General Chat mode: Using point-to-point encrypted communication, the service side has access to the key and can log in via multiple devices.
- Secret Chat mode: Encrypted communication using point-to-point can only be accessed through two specific devices.
The design combines some of the advantages of raiBlocks multi-chain construction with IOTA/Byteball DAG, which we call the Waring protocol. With improvements, we have given the WarRin protocol greater throughput and faster processing power while ensuring the security of the ledger, and network nodes can store the ledger in less space and search their communications accounts quickly in the ledger. When two users communicate, third parties contain content that neither manager can access. When a user is chatting in secret, the message contains multimedia that can be designated as a self-destruct message, and when the message is read by the user, the message is automatically destroyed within the specified time. Once the message expires, it disappears on the user’s device.
2.2 How chat history is encrypted
2.2.1 MTProto Transport Protocol
MTProto transport protocol
The WarRin communication system draws on RaiBlocks’ multi-chain structure for point-to-point communication. Each account has its own chain that records the sending and receiving behavior of the account. For example, in Figure 1, there are 7 accounts, each with 7 chain records of the account sending and receiving communications. On the graph, horizontal coordinates represent the timeline, and portrait coordinates represent the index of the account.
Transferring information from one account to another requires two transactions: one to send a communication from the sender’s transfer content, and one to receive information to add that content to the content of the receiving account. Whether in a send-side account or a receiving account, a PoW proof of work with the previous communication content Hash is required to add new communications to the account. In the account chain, poWwork proves to be an anti-spam communication tool that can be done in seconds. In a single account chain, the Hash field of the previous block is known to pre-generate the PoW required for subsequent blocks. Therefore, as long as the time between the two communications is greater than the time required to generate the PoW, the user’s transaction will be completed instantaneously.
In such a design, only the receiving end of the communication is required for settlement. The receiving end places the received communication signature on the account chain, which is called accepted communication. Once accepted, the receiving end then broadcasts the communication to the ledger of the other nodes. However, there may be situations where the receiving end is not online or is subject to a DoS attack, which prevents the receiving end from putting the receiving side communication on the account chain, which we call uncommoted transactions. The X symbol in Figure 1 represents an open transaction sent from Account 2 to Account 5.
Obviously, because only the sending and receiving sides of the communication are required to settle, such communication is very lightweight, all traffic can be transmitted in a UDP package and processed very quickly. At the same time, all communications in an account are kept in one chain, with great integrity, and the ledger can be trimmed to a minimum. Some nodes are not interested in spending resources to store the full communication history of the account; They are only interested in the current communications for each account. When an account communicates, its accumulated information is encoded, and these nodes only need to keep track of the latest blocks so that historical data can be discarded while maintaining correctness. Such communication is only possible if the sending and receiving sides trust each other and are not the final settlement of the entire network consensus. There is a security risk in the absence of trust on the sending and receiving ends, or in situations where the receiving end is attacked by DoS without the sender’s knowledge.
We have observed that although each account has a separate chain, the entire ledger can be expressed in the form of a WarRin object. As shown in Figure 2, this is represented by the WarRin astros trading on all accounts in Figure 1.
The first unit in the WarRin object is the Genesis unit, the next six cells represent the allocation of the initial token, and the other units correspond to the communication transactions between the account chains. We use the symbol a/b to represent a communication transaction, where the sender is a andthe recipient is b. The last 4/1 unit in Figure 2 is the last communication corresponding to Figure 1 – sending communication from account 4 to account 1. A transaction in Figure 1 is a confirmation of the latest block or the latest communication on the account chains of both parties to the communication, reflected in Figure 2 as a reference to the latest units of the account chains of both parties to the communication. Take unit 4/1, for example, where the latest block on account 4 was the receiving block for 2/4 trades and the newest block on account 1 was the send block for 1/5 trade. So on the DAG, the 4/1 cell refers to the 2/4 cell and the 1/5 cell.
The WarRin protocol uses triangular shrapned storage technology to crack impossible triangles in the blockchain through the shrapghine technology, with extensive node engagement and decontalination while maintaining high throughput and security:
- Complete shraping of blockchain status;
- Secure and low-cost cross-synth trading;
- Completely random witness selection;
- Flexible and efficient configuration
Complete decentralization ensures absolute security and scalability of the standard chain.
(Figures above show seven Ling-shaped objects:2/1 one;3/2 one… )
2.2.2 Curve25519 Elliptic Curve Encryption Algorithm
Curve25519, proposed by Daniel Bernstein, is anelliptic curve algorithm for the exchange of The Montgomery Curve’s Difi Herman keys.
Montgomery Curve Curve Mathematical Expression:
Curve25519 Curve Mathematical Expression:
Curve25519 encryption algorithms are used for standard private and public keys, and the private keys used for Curve25519
encryption algorithms are typically defined as secret
indices, corresponding to
public keys, coordinate points, which are usually sufficient to perform ECDH (elliptical) and symmetrical elliptic curve encryption algorithms. If one party wants to send information to the other party and the other party has the
public
and private keys, perform the following
calculation:
Generate a one-time random secret
index, calculated using Montgomery, because the message is a symmetrical password encrypted using 256-bit sharing, such as AES using a 256-bit integer
one-time public key, as akey, and 256-bit integer is a
prefix to encrypted information. Once a party to
the public
key receives this message, it can start by calculating , that is ,
the receiver recovers the shared secret and
is able to decrypt the rest of the information.
3. Incentives
On the basis of the WarRin agreement, by adding the incentive layer, we can effectively avoid the whole network being attacked and eliminate spam. As long as honest nodes control most of the calculations, for an attacker, the network is robust because of its simplicity of structure, and nodes need little coordination to work at the same time. They do not need to be authenticated because information is not sent to a location.
3.1 WRC Certificate
WRC issued a total of 2,500,000 pieces and continued to increment according to the WoRin gain function.
3.1.1 WoRin Gain Function
3.1.2 WoRin gain function control table
| The WoRin gain function is compared to the table | ||
| Number of layers /F | Growth factor /I | WRC circulation |
| [1,50] | 0.002 | 334918.8057 |
| [51,100] | 0.002 | 780024.2108 |
| [101,150] | 0.004 | 1177129.617 |
| [151,200] | 0.006 | 1487860.923 |
| [201,250] | 0.01 | 1722637 |
| [251,300] | 0.016 | 1894309.216 |
| [301,400] | 0.03 | 2101623.789 |
| [401,500] | 0.06 | 2217555.464 |
| [501,1000] | 0.1 | 2450712.257 |
| [1001,2000] | 0.12 | 2557457.3 |
According to the Gain function, the
larger the number of layers,
the greater the growth rate, the faster each layer is filled, and the
greater the circulation.
3.2 Allocation
WarRin protocol node distribution
3.2.1 Node allocation
Set the initial price
to 0.02,the layer where the first node is located is , according to the equation of the iso-difference column, there is , so that the
node token is assigned to the piece, for the price of
the layer where the node
is located, there is a
set.
For example, the number of tiers in which the 98th node is located is Tier 13, and the price of Tier 13 is 0.214,the tokens assigned by Tier 98 are
3.2.2 Total number of address assignments
Each node occupies one address, and the total number of addresses is
4. The use
WRC is the native pass-through of the WarRin protocol, andWRC will assign to Genesis nodes according to the above allocation scheme, which together form the entire network, andWRC can be used in the following scenarios, including but not limited to:
Pay the network’s gas charges, i.e. for transferring money and invoking smart contracts;
System Staking tokens, used for node elections and token issues;
The capital is lent to the validator in exchange for the amount of the reward;
Voting rights for system proposals;
The means of payment for apps developed on WoRin Services;
WoRin Storage is a means of payment on the decentralization storage;
WoRin DNS domain name and WoRin WWW website means of payment;
WoRin Proxy agents hide the means of payment for body and IP addresses;
WoRin Proxy penetrates payment methods reviewed by local ISPs
……
5. Conclusions
Metcalfe’s Law states that thevalue of a network is equal to the square of the number of nodes within the network, and that the value of the network is directly related to the square of the number of connected users. That is ( the
value factor, the number of
users.) That is, the greater the number of users on a network, the greater the value of the entire network and each computer within that network. The WarRin protocol also follows this law, and when the number of nodes reaches a certain level, the entire network becomes more robust.
References
[1] K. Birman, Reliable Distributed Systems: Technologies, Web Services and
Applications, Springer, 2005.
[2] V. Buterin, Ethereum: A next-generation smart contract and de- centralized
application platform, https://github.com/ethereum/wiki/wiki/White-Paper, 2013.
[3] M. Ben-Or, B. Kelmer, T. Rabin, Asynchronous secure computa- tions with
optimal resilience, in Proceedings of the thirteenth annual ACM symposium on
Principles of distributed computing, p. 183–192. ACM, 1994.
[4] M. Castro, B. Liskov, et al., Practical byzantine fault tolerance, Proceedings of the
Third Symposium on Operating Systems Design and Implementation (1999), p. 173–
186, available at http://pmg.csail.mit.edu/papers/osdi99.pdf.
[5] EOS. IO, EOS. IO technical white paper,
https://github.com/EOSIO/Documentation/blob/master/TechnicalWhitePaper.md,
2017.
[6] D. Goldschlag, M. Reed, P. Syverson, Onion Routing for Anony- mous and
Private Internet Connections, Communications of the ACM, 42, num. 2 (1999),
http://www.onion-router.net/Publications/CACM-1999.pdf.
[7] L. Lamport, R. Shostak, M. Pease, The byzantine generals problem, ACM
Transactions on Programming Languages and Systems, 4/3 (1982), p. 382–401.
[8] S. Larimer, The history of BitShares,
https://docs.bitshares.org/bitshares/history.html, 2013.
[9] M. Luby, A. Shokrollahi, et al., RaptorQ forward error correction scheme for
object delivery, IETF RFC 6330, https://tools.ietf.org/html/rfc6330, 2011.
[10] P. Maymounkov, D. Mazières, Kademlia: A peer-to-peer infor- mation system
based on the XOR metric, in IPTPS ’01 revised pa- pers from the First International
Workshop on Peer-to-Peer Systems, p. 53–65, available at
http://pdos.csail.mit.edu/~petar/papers/ maymounkov-kademlia-lncs.pdf, 2002.
About Author
Disclaimer: The views, suggestions, and opinions expressed here are the sole responsibility of the experts. No Digi Observer journalist was involved in the writing and production of this article.
Press Release
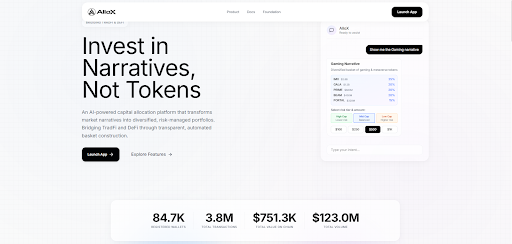
AlloX Launches AI-Powered Investment Platform with $25,000 USDT Prize Pool for Early Participants
British Virgin Islands, 27th February 2026, ZEX PR WIRE, AlloX is an AI-powered capital allocation platform recently launched and designed to help investors build diversified, risk-managed portfolios in the narrative-driven crypto market. It leverages artificial intelligence and automation to bridge TradFi and DeFi, enabling clear, transparent capital allocation.

AlloX is building the much-needed AI-driven allocation layer that crypto users can harness to invest in the narratives that drive the market, not in temporarily popular tokens. The platform soft-launched on February 23, and in only three days, it recorded over 3.8 million transactions, totaling over $123 million in volume and $751.3K in on-chain value from more than 84,700 connected wallets.
The crypto market has evolved into a standalone financial ecosystem where narrative drives liquidity allocation, transferring capital across multiple themes, including AI, gaming, RWA, DeFi, memecoins, etc. Despite these visible movements, many investors still allocate capital manually, and often react emotionally to volatility.
AlloX aims to solve this issue by making capital allocation structured, disciplined, and intelligent. The platform combines the primary traits of TradFi, such as portfolio construction and risk management, with fundamental DeFi features, such as transparency, automation, and permissionless access, to create a unique and powerful tool.
AlloX simplifies crypto investing by removing emotional trading and manual complexity. The crypto market is renowned for its swift shifts in attention between narratives. Therefore, instead of picking tokens one by one, users choose a narrative. Its AI-driven engine constructs a diversified basket based on that theme. It then applies transparent weights, selects a risk tier, and automatically rebalances depending on market movements. The entire process takes place transparently on the chain, allowing the user’s capital to flow in an organized, intelligent, and scalable way.
AlloX uses AI to analyze essential market data, including liquidity shifts, volatility metrics, sector performance, asset correlations, and narrative acceleration. It then automatically allocates capital to relevant investment targets. Users maintain autonomy by defining the narrative while AI drives capital distribution.
AlloX integrates portfolio analytics, allowing users to track their capital in real time across structured insights, such as Total Balance, Total Invested, Current Value, Profit and Loss, and Positions Overview.
The platform uses a points system to reward active users who engage with it and drive long-term growth. For instance, users earn points through the Welcome Bonus, portfolio creation, staking, completing X-related tasks, and the daily bonus.
The AlloX Daily Bonus is a new way for users to earn points just by logging in daily and claiming rewards. High consistency allows users to accrue more points, which count toward future airdrop eligibility.
The AI-driven capital allocation is the portfolio layer that AlloX brings to DeFi. The platform plans to add new layers, such as optimization, which integrates staking and yield-generating opportunities into the broader allocation framework to strengthen the AlloX ecosystem and drive participation.
Participation is one of the primary engines of the AlloX ecosystem. The platform launched The Spring Series, a 3-season campaign with $25,00 rewards, focused on growth, activity, and competitive progression.
AlloX AI Spring Warm Up is the first chapter of the Spring Series. It is designed to reward early participants, active users, and builders within the AlloX ecosystem, with a $5,000 USDT prize pool. Anyone can participate by connecting their wallets to AlloX, claiming their Welcome Bonus, and starting to earn points by completing tasks and being consistently active on the platform. This chapter started on February 23rd and will end on March 9th.
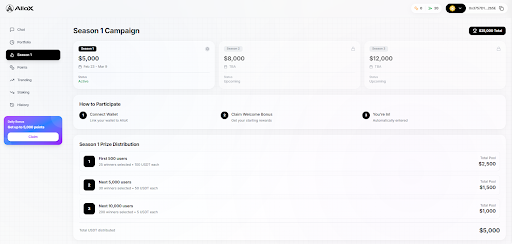
Following the Spring Warm Up, the AlloX Spring Series continues with two additional chapters: Spring Acceleration, featuring an $8,000 USDT prize pool, and Spring Finale, with a $12,000 USDT prize pool.
Early participants in the AlloX Spring Series benefit from several perks, including the opportunity to build strong momentum heading into the Finale chapter. More importantly, early users get to become more familiar with the platform before it reaches peak activity.
About AlloX
AlloX bridges the TradFi discipline with DeFi infrastructure through an AI-powered capital allocation platform that drives investment based on rapidly shifting market narratives. The platform eliminates time-consuming tasks, such as manual allocation, and relies on transparency and logic rather than emotional attachments to help investors build structured, diversified portfolios.
AlloX is designed by an experienced team with a proven track record in DeFi, including over $150 million in capital throughput, more than $100 million in allocated assets, and $40M+ in on-chain rewards. The team has a community reach of over 175,000 users, interacting with over 87,000 wallets while harnessing global liquidity from 10+ top-tier crypto exchanges.
Join AlloX today and start claiming your daily bonus, gathering points, and participating in the AlloX AI Spring Campaign for a share of the $25,000 USDT prize pool.
Learn more about AlloX by visiting its official website and social media pages: Telegram | X | LinkedIn | Instagram | Facebook |
About Author
Disclaimer: The views, suggestions, and opinions expressed here are the sole responsibility of the experts. No Digi Observer journalist was involved in the writing and production of this article.
Press Release
SPL VPN Leverages AI to Eliminate Manual Server Selection; Surpasses 2 Million Downloads in Connectivity Pivot

SINGAPORE, 27th February 2026, ZEX PR WIRE, SPL VPN, a leading provider of digital privacy solutions, today announced a major architectural transformation of its platform, integrating a proprietary AI-driven routing engine designed to eliminate the manual “server search” that has defined the VPN industry for over a decade. The update arrives as the company hits a significant growth milestone, surpassing 2 million global store downloads and maintaining a consistent user base of 500,000 daily active users.
Since its inception in 2018, SPL VPN has focused on the technical nuances of digital routing. This latest shift marks the retirement of traditional, manual server lists in favor of an intelligent, singular “Connect” protocol. By utilizing machine learning to handle complex routing decisions, SPL VPN is positioning itself as a “future-ready” utility in an increasingly automated digital landscape.
The Shift from Infrastructure to Intelligence
While the VPN industry has historically competed on “server counts,” SPL VPN is pivoting toward Zero-Touch Routing. The newly integrated AI engine performs real-time analysis of network congestion, local ISP throttling, and packet loss to construct a custom path for the user.
“The industry has spent years forcing users to navigate a paradox of choice, scrolling through thousands of servers to find a stable connection,” said the Head of Product at SPL. “We believe the future of the internet is an invisible, seamless layer. Our goal is to provide a utility that works efficiently before the user even realizes a connection bottleneck exists.”
Technical Milestones and Industry Impact
The ground-up architectural shift addresses three fundamental challenges in the legacy VPN market:
- Zero-Touch Efficiency: The AI identifies the most efficient path based on traffic type—optimizing specifically for high-bandwidth activities like 4K streaming and low-latency gaming without user intervention.
- Predictive Pathing: Unlike reactive services that wait for a connection to drop, SPL’s system anticipates node failures and reroutes traffic preemptively.
- Adaptive User Experience (UX): A streamlined interface designed for a digital-first audience, removing technical clutter to decrease the time-to-connection.
Eight Years of Strategic Refinement
SPL VPN’s evolution from a traditional privacy tool to an AI-enhanced utility follows eight years of silent refinement and data analysis. By moving away from the “infrastructure race” and focusing on routing intelligence, the company is catering to a modern web where speed and usability are as critical as encryption.
The updated platform reflects SPL’s commitment to making military-grade security accessible to casual users and technical professionals alike. With over half a million daily users already utilizing the service, SPL is demonstrating that the next phase of digital privacy is rooted in automation and effortless connectivity.
About SPL VPN
Founded in 2018 and headquartered in Singapore, SPL VPN is a global advocate for digital privacy and open-web access. By combining advanced encryption standards with cutting-edge AI research, SPL provides millions of users with a faster, safer, and more intuitive way to navigate the internet. With over 2 million downloads, SPL VPN continues to lead the shift toward intelligent, invisible security.
About Author
Disclaimer: The views, suggestions, and opinions expressed here are the sole responsibility of the experts. No Digi Observer journalist was involved in the writing and production of this article.
Press Release
Faith, Family, and Leadership: How Brent Byng Grounds His Approach to Success
Navarre, Florida, 27th February 2026, ZEX PR WIRE, In an era when organizations face constant disruption, shifting priorities, and growing demands on leaders, the most effective executives often draw strength from principles that extend beyond the workplace. For Brent Byng, a senior military leader and operations executive with more than 27 years of experience, faith, family, and service form the foundation of a leadership philosophy that has guided him through high-stakes environments, global responsibilities, and enterprise-scale operations.
Byng’s career spans joint special operations, national-level strategic leadership, and enterprise advisory roles. Across each chapter, he has remained grounded in values that emphasize accountability, humility, and responsibility to others. His approach demonstrates how personal principles can strengthen professional performance and provide clarity during complexity.
Leadership Anchored in Purpose
Throughout his career, Brent Byng has led organizations where decisions carried real consequences for people, missions, and outcomes. Whether managing enterprise budgets, advising senior leaders, or overseeing large, distributed teams, he has consistently emphasized purpose as the starting point for effective leadership.
Byng believes that leadership begins with service. This belief shaped his approach to command roles, policy assignments, and advisory positions. Rather than focusing solely on authority or position, he prioritizes stewardship, trust, and long-term impact.
Colleagues describe Byng as a leader who listens carefully, communicates clearly, and acts decisively. His leadership style reflects a balance between discipline and compassion, allowing teams to perform at a high level while remaining grounded in shared values.
Faith as a Source of Discipline and Perspective
Faith plays a central role in Byng’s leadership philosophy. He views faith not as a private compartment but as a source of discipline, reflection, and ethical clarity that informs his decisions.
Throughout decades of service, Byng relied on faith to maintain perspective during demanding assignments and periods of uncertainty. It shaped how he approached responsibility, accountability, and integrity, particularly when operating in environments defined by pressure and ambiguity.
Byng’s faith-based involvement includes participation in leadership formation programs focused on personal growth, responsibility, and service to others. These experiences reinforce principles such as humility, patience, and resilience, qualities that translate directly into effective leadership.
Rather than seeking recognition, Byng emphasizes consistency and character. He believes leaders earn trust through actions over time, guided by values that remain steady regardless of circumstance.
Family as the Foundation of Leadership
Family remains the cornerstone of Byng’s personal and professional life. He credits his family with providing balance, perspective, and motivation throughout his career.
Byng often speaks about leadership as an extension of responsibility learned at home. The lessons of commitment, accountability, and support that define strong families also define strong organizations. He believes leaders who honor family commitments bring greater empathy and stability to their professional roles.
During assignments that required long hours and frequent travel, Byng remained intentional about maintaining family connections. This discipline reinforced his belief that sustainable success requires balance rather than constant sacrifice.
By modeling these priorities, Byng encourages emerging leaders to define success in broader terms. He emphasizes that professional achievement should complement personal values rather than compete with them.
Service Before Self in Practice
Byng’s leadership philosophy reflects the principle of service before self, a value reinforced throughout his military career and carried into his enterprise leadership roles.
As a commander and senior operations leader, Byng prioritized the development and well-being of those he led. He consistently invested time in mentoring, coaching, and building leadership capacity across organizations.
His commitment to service extended beyond professional responsibilities. Byng has supported community initiatives, charitable efforts, and youth development programs. These efforts reflect his belief that leadership carries an obligation to contribute beyond organizational boundaries.
Service, in Byng’s view, strengthens credibility. Leaders who demonstrate genuine concern for others build trust that enables teams to navigate change and uncertainty more effectively.
Leading at Scale With Integrity
Over the course of his career, Byng has led organizations of more than 300 personnel and advised enterprises spanning multiple sites and departments. He has managed multimillion-dollar portfolios and supported leaders responsible for complex operational systems.
In each role, integrity served as a constant guide. Byng emphasizes transparency, ethical decision-making, and accountability as non-negotiable leadership standards.
As a senior advisor at Hurlburt Field, he provides strategic guidance across 12 departments, five geographic locations, and more than 1,600 personnel. His role requires aligning people, processes, and priorities while maintaining trust across diverse stakeholder groups.
Byng’s ability to lead at scale reflects not only technical expertise but also a values-based approach that fosters cohesion and resilience.
Faith and Decision-Making Under Pressure
Some of the most defining moments of Byng’s career occurred under intense pressure, where decisions carried operational, financial, and human consequences. In these moments, faith provided a framework for disciplined judgment.
Byng emphasizes preparation, reflection, and accountability when facing complex decisions. He avoids impulsive reactions and instead relies on structured analysis informed by experience and values.
This approach proved effective across operational command roles and strategic assignments at the Pentagon, where he supported senior defense leaders and international partners. His ability to remain composed and principled under pressure earned the trust of peers and superiors alike.
Faith, for Byng, reinforces the importance of responsibility over ego and mission over recognition.
Developing Leaders Through Values
Byng’s commitment to leadership development reflects his belief that values shape performance. Throughout his career, he has mentored mid-level and senior leaders, helping them build confidence, judgment, and ethical clarity.
He designed and supported leadership development and succession programs that emphasized competency, accountability, and personal growth. These programs strengthened organizational continuity and reduced reliance on individual personalities.
Byng encourages leaders to define their own guiding principles early and revisit them often. He believes values provide stability during change and prevent short-term pressures from undermining long-term goals.
This approach resonates with organizations seeking leaders who combine technical skill with character.
Academic and Professional Growth
Byng’s dedication to growth extends to his academic pursuits. He holds advanced degrees in operations management and military operational arts and science and continues to pursue a Doctor of Strategic Leadership.
His academic work reflects his interest in ethical leadership, organizational behavior, and strategic decision-making. Byng views education as a means of sharpening perspective and improving service to others.
Professional certifications in operations, project management, and human resources further support his ability to integrate people, systems, and strategy.
Byng’s commitment to learning underscores his belief that leadership requires continuous refinement rather than static expertise.
A Leadership Model for the Next Generation
As organizations confront rapid change and increasing complexity, Brent Byng’s leadership philosophy offers a compelling model. By grounding strategy and execution in faith, family, and service, he demonstrates that values-driven leadership remains relevant and effective.
His career illustrates that success does not require abandoning personal principles. Instead, Byng shows that strong values enhance decision-making, build trust, and sustain performance over time.
As he continues to advise leaders and position himself for senior executive opportunities, Byng brings a perspective shaped by decades of service, reflection, and responsibility.
In a world often focused on speed and scale, Brent Byng’s example reminds organizations that lasting success begins with grounded leadership rooted in faith, family, and purpose.
For more information, please feel free and visit https://brentbyng.com/
About Author
Disclaimer: The views, suggestions, and opinions expressed here are the sole responsibility of the experts. No Digi Observer journalist was involved in the writing and production of this article.
-
Press Release1 week ago
Nakuja Expeditions Offers All-Encompassing African Journeys Across Five Iconic Safari Destinations
-
Press Release6 days ago
First Class Demolition Expands Commercial Demolition Services Across Melbourne and Surrounding Suburbs
-
Press Release6 days ago
Bernardo Arsuaga Cardenas on Emerging Trends That Matter to Everyday People
-
Press Release7 days ago
Los Angeles Marketing Strategist Sedrick Sparks Says Sustainability and Ethical Marketing Now Define Brand Survival
-
Press Release1 week ago
McLaren Charlotte Launches a Personal Pledge for Informed Performance Culture
-
Press Release6 days ago
AgriFi Launches Real Yield DeFi Platform Backed by Agricultural Productivity
-
Press Release1 week ago
HydraMeshnet Launches Commercially Available Off-Grid Mesh Network Infrastructure as Global Blackouts Expose Systemic Network Fragility
-
Press Release6 days ago
Tennessee-born Marketing Strategist, John Gordon Nutley, on Budget Constraints and Digital Challenges Facing SMEs



