Press Release
WarRin Protocol: A point-to-point anonymous privacy communication system
Dr.WarRin
Summary
This white paper provides an explanation of the WarRin protocol and related blockchain, point-to-point, network value, transport protocol, and encryption algorithms. The limited space will highlight the WRC allocation scheme and purpose of the WarRin Protocol Token, which is important for achieving the WRC’s stated objectives. This white paper is for informational purposes only and is not a promise of final implementation details. Some details may change during the development and testing phases.
1. Introduction
Traditional centralized communication systems such as WeChat,WhatsApp, FacebookMessage,Google Allo,Skype face a range of problems, including government surveillance, privacy breaches, and inadequate security, and the WarRin protocol proposes apoint-to-pointencrypted communications system that leveragesblockchain technology, combined with Double Ratc het algorithms, pre-keys, and extended X3DH handshakes. The WarRin Protocol uses The Generalized Directional Acyclic Graph and Curve25519,AES-256, and HMAC-SHA256 as the pronamor, allowing each account to have its own unique account chain, providing unlimited instant communication between points and unlimited scalability, anonymity, integrity, consistency, and asynchronousness.
2. WarRin Protocol communication system
2.1 Two types of communication
The Waring Protocol communication system divides chat channels into two types.
Two modes of communication
- General Chat mode: Using point-to-point encrypted communication, the service side has access to the key and can log in via multiple devices.
- Secret Chat mode: Encrypted communication using point-to-point can only be accessed through two specific devices.
The design combines some of the advantages of raiBlocks multi-chain construction with IOTA/Byteball DAG, which we call the Waring protocol. With improvements, we have given the WarRin protocol greater throughput and faster processing power while ensuring the security of the ledger, and network nodes can store the ledger in less space and search their communications accounts quickly in the ledger. When two users communicate, third parties contain content that neither manager can access. When a user is chatting in secret, the message contains multimedia that can be designated as a self-destruct message, and when the message is read by the user, the message is automatically destroyed within the specified time. Once the message expires, it disappears on the user’s device.
2.2 How chat history is encrypted
2.2.1 MTProto Transport Protocol
MTProto transport protocol
The WarRin communication system draws on RaiBlocks’ multi-chain structure for point-to-point communication. Each account has its own chain that records the sending and receiving behavior of the account. For example, in Figure 1, there are 7 accounts, each with 7 chain records of the account sending and receiving communications. On the graph, horizontal coordinates represent the timeline, and portrait coordinates represent the index of the account.
Transferring information from one account to another requires two transactions: one to send a communication from the sender’s transfer content, and one to receive information to add that content to the content of the receiving account. Whether in a send-side account or a receiving account, a PoW proof of work with the previous communication content Hash is required to add new communications to the account. In the account chain, poWwork proves to be an anti-spam communication tool that can be done in seconds. In a single account chain, the Hash field of the previous block is known to pre-generate the PoW required for subsequent blocks. Therefore, as long as the time between the two communications is greater than the time required to generate the PoW, the user’s transaction will be completed instantaneously.
In such a design, only the receiving end of the communication is required for settlement. The receiving end places the received communication signature on the account chain, which is called accepted communication. Once accepted, the receiving end then broadcasts the communication to the ledger of the other nodes. However, there may be situations where the receiving end is not online or is subject to a DoS attack, which prevents the receiving end from putting the receiving side communication on the account chain, which we call uncommoted transactions. The X symbol in Figure 1 represents an open transaction sent from Account 2 to Account 5.
Obviously, because only the sending and receiving sides of the communication are required to settle, such communication is very lightweight, all traffic can be transmitted in a UDP package and processed very quickly. At the same time, all communications in an account are kept in one chain, with great integrity, and the ledger can be trimmed to a minimum. Some nodes are not interested in spending resources to store the full communication history of the account; They are only interested in the current communications for each account. When an account communicates, its accumulated information is encoded, and these nodes only need to keep track of the latest blocks so that historical data can be discarded while maintaining correctness. Such communication is only possible if the sending and receiving sides trust each other and are not the final settlement of the entire network consensus. There is a security risk in the absence of trust on the sending and receiving ends, or in situations where the receiving end is attacked by DoS without the sender’s knowledge.
We have observed that although each account has a separate chain, the entire ledger can be expressed in the form of a WarRin object. As shown in Figure 2, this is represented by the WarRin astros trading on all accounts in Figure 1.
The first unit in the WarRin object is the Genesis unit, the next six cells represent the allocation of the initial token, and the other units correspond to the communication transactions between the account chains. We use the symbol a/b to represent a communication transaction, where the sender is a andthe recipient is b. The last 4/1 unit in Figure 2 is the last communication corresponding to Figure 1 – sending communication from account 4 to account 1. A transaction in Figure 1 is a confirmation of the latest block or the latest communication on the account chains of both parties to the communication, reflected in Figure 2 as a reference to the latest units of the account chains of both parties to the communication. Take unit 4/1, for example, where the latest block on account 4 was the receiving block for 2/4 trades and the newest block on account 1 was the send block for 1/5 trade. So on the DAG, the 4/1 cell refers to the 2/4 cell and the 1/5 cell.
The WarRin protocol uses triangular shrapned storage technology to crack impossible triangles in the blockchain through the shrapghine technology, with extensive node engagement and decontalination while maintaining high throughput and security:
- Complete shraping of blockchain status;
- Secure and low-cost cross-synth trading;
- Completely random witness selection;
- Flexible and efficient configuration
Complete decentralization ensures absolute security and scalability of the standard chain.
(Figures above show seven Ling-shaped objects:2/1 one;3/2 one… )
2.2.2 Curve25519 Elliptic Curve Encryption Algorithm
Curve25519, proposed by Daniel Bernstein, is anelliptic curve algorithm for the exchange of The Montgomery Curve’s Difi Herman keys.
Montgomery Curve Curve Mathematical Expression:
Curve25519 Curve Mathematical Expression:
Curve25519 encryption algorithms are used for standard private and public keys, and the private keys used for Curve25519
encryption algorithms are typically defined as secret
indices, corresponding to
public keys, coordinate points, which are usually sufficient to perform ECDH (elliptical) and symmetrical elliptic curve encryption algorithms. If one party wants to send information to the other party and the other party has the
public
and private keys, perform the following
calculation:
Generate a one-time random secret
index, calculated using Montgomery, because the message is a symmetrical password encrypted using 256-bit sharing, such as AES using a 256-bit integer
one-time public key, as akey, and 256-bit integer is a
prefix to encrypted information. Once a party to
the public
key receives this message, it can start by calculating , that is ,
the receiver recovers the shared secret and
is able to decrypt the rest of the information.
3. Incentives
On the basis of the WarRin agreement, by adding the incentive layer, we can effectively avoid the whole network being attacked and eliminate spam. As long as honest nodes control most of the calculations, for an attacker, the network is robust because of its simplicity of structure, and nodes need little coordination to work at the same time. They do not need to be authenticated because information is not sent to a location.
3.1 WRC Certificate
WRC issued a total of 2,500,000 pieces and continued to increment according to the WoRin gain function.
3.1.1 WoRin Gain Function
3.1.2 WoRin gain function control table
| The WoRin gain function is compared to the table | ||
| Number of layers /F | Growth factor /I | WRC circulation |
| [1,50] | 0.002 | 334918.8057 |
| [51,100] | 0.002 | 780024.2108 |
| [101,150] | 0.004 | 1177129.617 |
| [151,200] | 0.006 | 1487860.923 |
| [201,250] | 0.01 | 1722637 |
| [251,300] | 0.016 | 1894309.216 |
| [301,400] | 0.03 | 2101623.789 |
| [401,500] | 0.06 | 2217555.464 |
| [501,1000] | 0.1 | 2450712.257 |
| [1001,2000] | 0.12 | 2557457.3 |
According to the Gain function, the
larger the number of layers,
the greater the growth rate, the faster each layer is filled, and the
greater the circulation.
3.2 Allocation
WarRin protocol node distribution
3.2.1 Node allocation
Set the initial price
to 0.02,the layer where the first node is located is , according to the equation of the iso-difference column, there is , so that the
node token is assigned to the piece, for the price of
the layer where the node
is located, there is a
set.
For example, the number of tiers in which the 98th node is located is Tier 13, and the price of Tier 13 is 0.214,the tokens assigned by Tier 98 are
3.2.2 Total number of address assignments
Each node occupies one address, and the total number of addresses is
4. The use
WRC is the native pass-through of the WarRin protocol, andWRC will assign to Genesis nodes according to the above allocation scheme, which together form the entire network, andWRC can be used in the following scenarios, including but not limited to:
Pay the network’s gas charges, i.e. for transferring money and invoking smart contracts;
System Staking tokens, used for node elections and token issues;
The capital is lent to the validator in exchange for the amount of the reward;
Voting rights for system proposals;
The means of payment for apps developed on WoRin Services;
WoRin Storage is a means of payment on the decentralization storage;
WoRin DNS domain name and WoRin WWW website means of payment;
WoRin Proxy agents hide the means of payment for body and IP addresses;
WoRin Proxy penetrates payment methods reviewed by local ISPs
……
5. Conclusions
Metcalfe’s Law states that thevalue of a network is equal to the square of the number of nodes within the network, and that the value of the network is directly related to the square of the number of connected users. That is ( the
value factor, the number of
users.) That is, the greater the number of users on a network, the greater the value of the entire network and each computer within that network. The WarRin protocol also follows this law, and when the number of nodes reaches a certain level, the entire network becomes more robust.
References
[1] K. Birman, Reliable Distributed Systems: Technologies, Web Services and
Applications, Springer, 2005.
[2] V. Buterin, Ethereum: A next-generation smart contract and de- centralized
application platform, https://github.com/ethereum/wiki/wiki/White-Paper, 2013.
[3] M. Ben-Or, B. Kelmer, T. Rabin, Asynchronous secure computa- tions with
optimal resilience, in Proceedings of the thirteenth annual ACM symposium on
Principles of distributed computing, p. 183–192. ACM, 1994.
[4] M. Castro, B. Liskov, et al., Practical byzantine fault tolerance, Proceedings of the
Third Symposium on Operating Systems Design and Implementation (1999), p. 173–
186, available at http://pmg.csail.mit.edu/papers/osdi99.pdf.
[5] EOS. IO, EOS. IO technical white paper,
https://github.com/EOSIO/Documentation/blob/master/TechnicalWhitePaper.md,
2017.
[6] D. Goldschlag, M. Reed, P. Syverson, Onion Routing for Anony- mous and
Private Internet Connections, Communications of the ACM, 42, num. 2 (1999),
http://www.onion-router.net/Publications/CACM-1999.pdf.
[7] L. Lamport, R. Shostak, M. Pease, The byzantine generals problem, ACM
Transactions on Programming Languages and Systems, 4/3 (1982), p. 382–401.
[8] S. Larimer, The history of BitShares,
https://docs.bitshares.org/bitshares/history.html, 2013.
[9] M. Luby, A. Shokrollahi, et al., RaptorQ forward error correction scheme for
object delivery, IETF RFC 6330, https://tools.ietf.org/html/rfc6330, 2011.
[10] P. Maymounkov, D. Mazières, Kademlia: A peer-to-peer infor- mation system
based on the XOR metric, in IPTPS ’01 revised pa- pers from the First International
Workshop on Peer-to-Peer Systems, p. 53–65, available at
http://pdos.csail.mit.edu/~petar/papers/ maymounkov-kademlia-lncs.pdf, 2002.
About Author
Disclaimer: The views, suggestions, and opinions expressed here are the sole responsibility of the experts. No Digi Observer journalist was involved in the writing and production of this article.
Press Release
Qtum Launches Comprehensive AI Infrastructure Stack with Text-to-Video and Unified AI Access
A long‑running Bitcoin‑based smart contract platform evolves into a modern AI and compute ecosystem
Singapore, June 4th, 2026, Qtum Foundation- Qtum today announced the expansion of its ecosystem with Qtum.ai, a text‑to‑video generation platform, and the upcoming Qtum AI Router, a unified inference layer designed to provide efficient access to multiple AI models. Together, these services position Qtum as a blockchain‑supported AI infrastructure network built on a stable, long‑running Proof‑of‑Stake blockchain that has operated continuously since 2017.
Qtum’s approach combines its Bitcoin‑based UTXO architecture, EVM‑compatible smart contracts, and a reliable, production‑ready blockchain with modern AI tooling, GPU compute, and creator‑focused workflows. The result is an ecosystem that spans blockchain infrastructure, decentralized compute, and AI generation tools under a single brand.
Qtum.ai: Text‑to‑Video for Creators and Developers
Qtum.ai provides cinematic text‑to‑video generation using models such as Seedance 1.0, 1.5, and 2.0 and HappyHorse. The platform is designed for creators, developers, and businesses seeking high‑quality AI video without subscription barriers.
Key characteristics include:
-
- No credit card required
- No recurring subscription
- No token packs or prepaid bundles
- Pay‑as‑you‑go usage
- No data harvesting or model training on user content
- No cookies, tracking pixels, or ad‑retargeting
- Authentication via MetaMask Snap or Google login
- 500 Free tokens
This model removes common friction points in AI services, including subscription lock‑in, credit‑card anxiety, and persistent marketing emails. Users can generate videos without entering financial information or committing to monthly plans.
Qtum AI Router: A Unified Inference Layer
Beta Launching will be the Qtum AI Router to provide a unified API for routing requests across multiple AI models. Similar in concept to OpenRouter, the service will support:
- AI model routing
- Multi‑model inference
- Distributed GPU compute
- Low‑latency request handling
- AI orchestration and workflow integration
- Agent‑compatible infrastructure
The Router is designed to support developers building AI agents, automation tools, and multi‑model applications. ClawBot users will find this simple to work with.
A Blockchain With Long‑Term Reliability
Qtum’s blockchain has operated since 2017 with no downtime, offering a stability profile uncommon in the industry. The network combines:
-
- Bitcoin‑based UTXO security
- EVM‑compatible smart contracts
- Proof‑of‑Stake consensus
- Enterprise‑grade reliability
- Consistent uptime across seven years of operation
- 50 Core updates over 8 years
This reliability is central to Qtum’s positioning as an AI compute network. AI services require predictable, uninterrupted operation — a requirement Qtum’s blockchain has demonstrated over years of production use.
A Unified Ecosystem: Blockchain + AI + Compute
The Qtum ecosystem now spans:
- Qtum blockchain — a long‑running, stable, Bitcoin‑based smart contract platform
- Qtum.ai — AI video generation for creators and businesses
- Qtum AI Router — unified inference routing for multi‑model AI
- Qtum Ally — a desktop AI agent integrating multiple LLMs
- GPU infrastructure — powering inference and generation workloads
This positions Qtum as a hybrid blockchain and AI infrastructure network, supporting decentralized compute, creator tools, and useful Web3 applications.
About Qtum
Qtum is a Proof‑of‑Stake blockchain that combines Bitcoin’s UTXO model with Ethereum‑compatible smart contracts. Launched in 2017, Qtum has maintained uninterrupted network operation for over seven years. Today, Qtum is expanding into AI infrastructure, GPU compute, and creator‑focused tooling through Qtum.ai and the Qtum AI Router.
Website: https://qtum.ai
About Author
Disclaimer: The views, suggestions, and opinions expressed here are the sole responsibility of the experts. No Digi Observer journalist was involved in the writing and production of this article.
Press Release
Snagle Paw Introduces Premium Mobility and Home Safety Solutions for Modern Pet Families
Designed for daily pet care needs, Snagle Paw’s StrideMate Series bring together outdoor mobility and safer indoor management for large, senior, injured, disabled, and multi-dog households.
Sheridan, Wyoming, United States, 4th Jun 2026 – As more pet owners seek practical ways to support aging, injured, or large dogs, mobility and home safety products are becoming increasingly important in modern pet care. Snagle Paw, a premium pet brand serving pet families since 2012, has introduced a focused range of pet mobility and home safety solutions designed around real household needs.
The product line addresses two common care scenarios: helping dogs continue outdoor routines more comfortably and supporting safer indoor management near doors, stairs, hallways, and other high-risk areas.

Practical Needs in Everyday Pet Care
Many pet owners face challenges when caring for large dogs, senior pets, injured animals, disabled dogs, or households with more than one dog.
Traditional pet strollers may offer limited space, lower weight capacity, or difficult access for heavier dogs. At home, energetic or curious pets may rush toward doors, stairways, or busy entrances when a reliable barrier is not in place.
Snagle Paw’s latest solutions are designed to support these everyday situations with products that combine mobility, space, safety, and ease of use.
Stroller Wagons Designed for Larger and Mobility-Limited Dogs
Among the brand’s outdoor mobility solutions, the StrideMate Max is a large dog stroller wagon designed for large, senior, injured, and disabled dogs that need more room and easier access than many standard pet strollers provide.
Its stroller-wagon format offers a more practical option for dogs that may struggle with long walks, recovery outings, or travel.

The StrideMate Pro also serves as a practical dog stroller for large dogs and multi-dog households seeking higher weight capacity and more spacious travel support.
Both stroller wagons support up to 220 lbs and include a spacious cabin that allows dogs to turn around, sit comfortably, or lie down and rest during outdoor use.
A defining feature of the stroller wagons is the built-in ramp, which allows dogs to walk in and out without being lifted. This design can help reduce strain for senior, injured, or disabled pets while making daily outings more manageable for owners.
The built-in canopy provides shade from sunlight and protection from light rain, reflecting Snagle Paw’s original approach to combining comfort, protection, and practical pet mobility.

Retractable Metal Gate Supports Safer Home Environments
For indoor safety, the Extra-Tall Metal Retractable Dog Gate is designed to help prevent dogs from rushing out when doors are opened. It is intended for use near front doors, stairs, hallways, apartment corridors, and other areas where pet owners may need a temporary but dependable safety barrier.
The gate’s retractable design allows families to create a boundary when needed and store it neatly when not in use. Its metal construction provides stronger support, greater durability, and a more secure feel compared with many soft mesh or lightweight barriers.
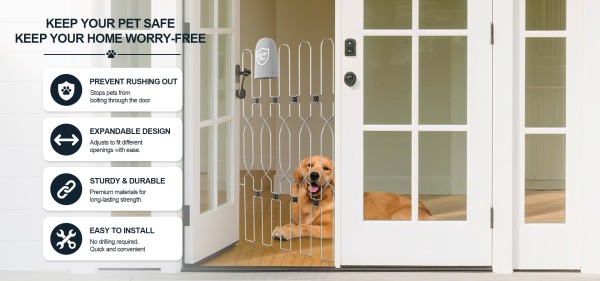
“Snagle Paw was born from real family needs. We wanted to create products that solve everyday problems for pet parents, from helping large or senior dogs get outside more comfortably to preventing energetic dogs from rushing out the door at home. Features like the built-in ramp, 220-lb weight capacity, spacious cabin, protective canopy, retractable design, and durable metal structure reflect our commitment to making pet care safer, easier, and more comfortable,” said a spokesperson for Snagle Paw.
Building on this philosophy, Snagle Paw plans to continue developing pet-care products inspired by real family routines, with an ongoing focus on safety, comfort, flexibility, and everyday usability for pets and their owners.
Snagle Paw’s R&D team is continuously expanding their portfolio of innovative solutions designed to support senior and injured dogs. Upcoming releases will include dog leg braces, lift harnesses, red light therapy harnesses and pads, as well as PEMF dog beds—further reinforcing our commitment to enhancing canine mobility, comfort, and overall well-being.
Learn more info about Snagle Paw’s official website and social media:
Facebook: https://www.facebook.com/snaglepaw.official/
Instagram: https://www.instagram.com/snaglepaw
YouTube: https://www.youtube.com/@SnaglePaw
TikTok: https://www.tiktok.com/@snaglepaw
About Snagle Paw
Snagle Paw is a premium pet brand created for pet families since 2012. Inspired by real pets and real family needs, the brand develops thoughtfully designed products that help pets enjoy safety, comfort, and freedom at home and on the go.
With product lines covering dog stroller wagons, retractable dog gates, travel crates, and other pet lifestyle solutions, Snagle Paw is dedicated to helping owners care for their furry companions with greater ease, confidence, and warmth.
Media Contact
Organization: Snagle Paw
Contact Person: Kevin Yan
Website: https://snaglepaw.com/
Email:
info@snaglepaw.com
Contact Number: +13073818630
Address:Snagle International Inc, 30 N Gould St Ste R, Sheridan, WY 82801, USA
City: Sheridan
State: Wyoming
Country:United States
Release id:45715
The post Snagle Paw Introduces Premium Mobility and Home Safety Solutions for Modern Pet Families appeared first on King Newswire. This content is provided by a third-party source.. King Newswire makes no warranties or representations in connection with it. King Newswire is a press release distribution agency and does not endorse or verify the claims made in this release. If you have any complaints or copyright concerns related to this article, please contact the company listed in the ‘Media Contact’ section
About Author
Disclaimer: The views, suggestions, and opinions expressed here are the sole responsibility of the experts. No Digi Observer journalist was involved in the writing and production of this article.
Press Release
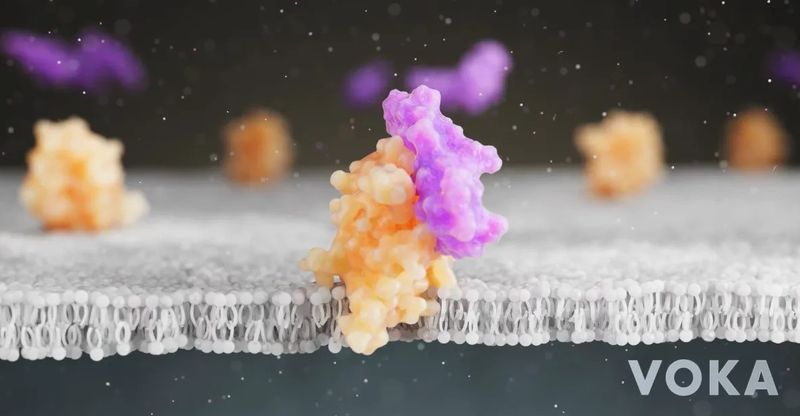
VOKA Receives Bronze at the Telly Awards 2026
Medical visualization company VOKA won a Bronze Award at the 47th Annual Telly Awards for its 3D animation, “Mechanism of Semaglutide: The Science Behind Fat Loss. The award-winning 3D medical animation “Mechanism of Semaglutide” visualizes complex metabolic processes with cinematic precision
New York, United States, June 4, 2026 — VOKA’s video “Mechanism of Semaglutide: The Science Behind Fat Loss” has been awarded Bronze at the 47th Annual Telly Awards in the “General-Healthcare & Medical” category.
The awards honor excellence in video and television production across multiple platforms and are judged by leaders from video platforms, television, streaming networks, and production companies. This year’s winners include Paramount TV, Warner Brothers Discovery, FOX Entertainment, Sony Music, TED, ABC News, and many others.
The recognition highlights VOKA’s work in producing scientifically accurate 3D medical animations that help explain complex biological and therapeutic processes.
About VOKA’s Project
The winning animation, “Mechanism of Semaglutide: The Science Behind Fat Loss,” visualizes how semaglutide regulates metabolism and appetite. The video specifically highlights key biological steps, including POMC/CART activation (triggering the sense of satiety), NPY/AgRP reduction (leading to a decrease in cravings), and vagus nerve interaction to slow gastric emptying.
By explaining these complex scientific concepts through an engaging, clear narrative, the video serves as an ideal tool for medical education, pharmaceutical marketing, and scientific communication.
The award-winning animation can be viewed here: https://youtu.be/zUsf09RrkTM?si=IksqZm4FUCVZlszv
About the Award
Established in 1979, the Telly Awards is a global competition created to honor excellence in television and digital video production. Submissions are evaluated by the Telly Awards Judging Council, a panel of over 250 industry professionals from giants like the BBC, Amazon, and Netflix. Entries are assessed based on creativity, storytelling, and the innovative use of technology across various media platforms.
About VOKA
VOKA is one of the leading providers of high-fidelity medical visualization and immersive technologies, delivering a comprehensive suite of 3D medical and scientific animation services for the pharmaceutical, life sciences, and medical education sectors. The company specializes in tailored 3D animations across diverse therapeutic fields — including cardiology, dermatology, oncology, and urology — as well as high-precision depictions of Mechanisms of Action (MoA), Mechanisms of Disease (MoD), medical devices, and surgical procedures.
To bridge the gap between complex science and engaging storytelling, VOKA combines the expertise of an in-house medical team with professional 3D artists and motion designers, ensuring cinematic-quality visuals that maintain the highest scientific accuracy and regulatory compliance. Beyond animation production, VOKA develops interactive 3D anatomy and pathology models and extended reality (XR) experiences to elevate clinical training and medical communication worldwide.
Contact Info:
Name: Maryia Shchakovich
Email: info@voka.io
Organization: VOKA
Website: https://voka.io/
About Author
Disclaimer: The views, suggestions, and opinions expressed here are the sole responsibility of the experts. No Digi Observer journalist was involved in the writing and production of this article.
-
Press Release6 days ago
2026 BRICS New Industrial Revolution Partnership Forum Opened in Xiamen
-
Press Release1 week ago
A Tribute to DJ Kay Slay — From JDLINO Brand, Friends, and FELITWO
-
Press Release1 week ago
GCL Announces the Global Console and PC Version 1.0 Release of ‘Realm of Ink’
-
Press Release5 days ago
Creality Printers Review Site Helps Buyers Compare Creality Printers
-
Press Release6 days ago
Streamex Adds Microsoft and PayPal Lead Product Designer to High Level Talent Roster
-
Press Release6 days ago
Katana Bridge Guide 2026: Secure Cross-Chain Transfers Made Simple
-
Press Release5 days ago
Birmingham Loft Conversions Experts Help Homeowners Unlock Hidden Space
-
Press Release6 days ago
Good Good Creative Leads Video Production Excellence in Hong Kong to Drive Brand Growth



